Bot Farms a Billion Dollar Industry & How to Unravel their Black Magic
PPC click fraud is a gigantic industry that’s growing rapidly. It is estimated that the global click fraud market will cross $44 billion by 2022 with up to 14% of all PPC spending estimated to be invalid. Click fraud is a reality that advertisers, marketers, and businesses are living with. Whether it be bot farms, click bots, or any other type of PPC click fraud, it is there. You can’t deny it. You keep wasting money on such fraudulent clicks assuming your campaigns aren’t delivering and these clicks frustrate your business goals.
PPC click fraud has a long history and to safeguard your ads from it, you need to understand the basics of how click fraud works, what are the types of invalid clicks, why they exist in the first place, and what (if any) steps you can take to avoid invalid clicks, bot farms, and click bots.
This article covers everything in detail.
What is a PPC Invalid Click?
An invalid click is an illegitimate click that’s either unintentional or generates from malicious software. Invalid clicks cost you money resulting in a high CTR and cost but no conversions as invalid clicks don’t convert.
Invalid clicks are either generated by your competitors to exhaust your budget or by the ad publisher to increase the revenue. Sophisticated software is used to generate invalid clicks at a massive level to ensure transparency and to go undetected.
Invalid clicks could be manual, accidental, or automated. Accidental and manual clicks aren’t as harmful as they’re easy-to-detect. Google Ads, for example, is great at detecting invalid clicks that deliver no value to the advertiser and it has a strict policy on invalid clicks.
Invalid clicks could be manual, accidental, or automated.
The problem is with automated invalid clicks that are generated by software, malware, and scripts, and are extremely hard to detect. This is where things get complicated. These clicks are generated by sophisticated software that copies human behaviour and looks real. Alternately, there are real people, not bots who generate invalid clicks. This makes things more complicated and detecting these types of invalid clicks generated by real humans is no easy task.

A bot farm or a click bot is a script, malware, or a piece of software that generates clicks automatically by creating fake IP addresses and web sessions. But this is just the beginning…
Let’s dig deep…
Bot Farms and Invalid Clicks
A bot farm is a system or farm of bots that are used to generate clicks and internet traffic. These bots are used extensively for various purposes and not just invalid PPC clicks. For example, bot farms are known to be used in app stores to improve app rankings.
Here is an example of how one app developer shared his story of how an ad network told him that they have a huge bot farm to promote his new app. The bots download the app automatically that improves the ranking of the app in the store.
Interestingly, the bot farm owner shared how leading top app owners were using his bot farms.
This was 2012…
Things have become worse since then.
Today, there are several types of bot farms that generate invalid clicks that usually go undetected and are hard to catch. The bot farms today adapt and scale aggressively due to machine learning. A recently detected bot farm called Methbot resulted in up to $5 million in losses to advertisers per day.
It is a gigantic industry that’s growing fast.
A bot farm isn’t just a simple script anymore rather it is a complete software with dedicated infrastructure consisting of servers, data centres, several connected computers, routers, and more. A bot farm uses sophisticated technical equipment and advanced structuring and coding to generate heaps of invalids clicks on a daily basis.
To give you an idea of how sophisticated today’s bot farms are, the Security Service of Ukraine recently found a Russian bot farm and confiscated equipment that was used by the bot farm. The equipment included two telecommunication companies, computers, telecommunication hardware, 22,000+ sim cards, and other equipment. A similar bot farm was detected in 2016 by Ukrainian Cyber Police that included 4,000+ servers located in 63 countries.
The Methbot claimed to be the biggest and most devastating bot farm ever detected, had its servers and data centres located in Dallas and Amsterdam. A single server runs multiple sessions of the bot farm and it has around 1200 servers. The Methbot had more than 852,991 IP addresses that were generated using false registration details to make them appear real. Just to give you an idea of the scale, Facebook uses only 400,000 IP addresses while Methbot had 2x more.
This is the scale at which bot farms operate and generate invalid clicks to your PPC campaigns.
Botnets
A botnet is a system of connected devices (e.g. computers and routers) that are infected by malware and hackers can control the whole network or connected devices without the owner’s knowledge.
A botnet can be used by hackers to generate invalid clicks on PPC campaigns. In this case, hackers leverage existing infrastructure to generate invalid clicks and other online activities.
Large bot farms consist of both botnets and their own infrastructure (e.g. servers). Sophisticated and large bot farms have their own private IT infrastructure making them hard to detect.
Generally, a bot farm is a combination of both.
Are Bot Farms and Click Bots the Same?

Technically, a bot farm is more sophisticated than a click bot. Click bots are programmed software or a script that is specifically used for generating invalid clicks and is used widely in the PPC industry. Click bots aren’t as sophisticated and backed by massive infrastructure like a bot farm, but a decent and well-programmed click bot is capable of much more than you can imagine.
A bot farm doesn’t just generate clicks rather it is capable of doing much more than merely generating invalid clicks and impressions.
A simple click bot will click an ad and visit the landing page. A well-designed and robust click bot will replicate human behaviour and will take several actions on the landing page e.g. scrolling, filling the form, mouse movement, multiple clicks, etc.
A more advanced version of click bot will learn and evolve. These are adaptable click bots that use machine learning for evolution.
Click bots can be purchased or developed inhouse to be used to generate invalid clicks on competitor PPC ads. However, most of the click bots are malware that spread automatically and are part of a botnet or a bot farm. The malware click bots receive specific instructions on what ads to click, how much time to spend on the landing page, what actions to take on the landing page, etc. from the botmaster server.
The botmaster and the click bots act as a network that can be used to generate fake PPC clicks across multiple campaigns and ad networks.
Clickbot.A is a popular malware click bot that was identified as a trojan by anti-virus programs. It used to get instructions from the botmaster server and used to click ads as instructed. It is used to develop a loop clicking the ad once every 15 minutes.
These types of sophisticated click bots that are part of a bigger botnet are hard to detect and usually go unnoticed.
How Bot Farms Drive Invalid Clicks
There isn’t any single best way how these bot farms generate invalid clicks. In fact, they come up with new and better ways to drive invalid clicks every single time. Once a bot farm and its approach are detected, hackers don’t use the same technique again. Rather, they evolve and come up with a better technique and infrastructure.
It is a new game every single day.
And this is how bot farms and their clicks go unnoticed – they evolve. At the backend of every bot farm, there are real humans who keep learning and getting better with time.
However, the secret sauce of any bot farm is none other than the IP address. No matter how advanced and adaptable bot farms and hackers become, they can’t run their farm without IP addresses.
Why?
An IP address is a unique numerical identity or label assigned to each hardware or device that’s connected to a network or the internet. The IP address is used to identify devices and that’s how data is transferred among devices on the internet.
An IP address is used to identify devices on the internet and the location of the device. Bot farms can’t run without IP addresses. They’ll either use other people’s devices by hacking them (in case of a botnet) or they’ll have their own computers and servers. In both cases, each device in the network will have an IP address.
However, bot farms have fake IP addresses to keep their network and location hidden.
Once you have an IP address, your activity on the internet will be tracked and this is how bot farms drive invalid clicks. Having several fake IP addresses, they click on the ads and have their clicks counted. In the absence of an IP address (hypothetically), a bot farm won’t be able to drive invalid clicks because clicks without IP addresses aren’t tracked and won’t be counted.
The whole idea of driving invalid clicks is to get the click noticed and counted. And this makes IP addresses a goldmine for bot farms and click bots. Once they have fake IP addresses, they can proceed with the invalid clicks.
This is a reason why hackers prefer hacking networks and devices. They can generate invalid clicks using other people’s IP addresses without ever getting themselves noticed. Even if the IP address is tracked somehow, the hacker will move with the malware to another network or device.
The bot farms usually have their own servers and hardware, so the farm uses fake IP addresses to drive clicks on complete autopilot. Sophisticated bot farms use proxies and IP diversity. Registration falsifying is a common practice to make IP addresses appear legit. In fact, large bot farms use whole ISPs like Comcast to create IP addresses with full registration details. Then thousands of these IP addresses are used with proxies to go undetected providing the bot farm with the capacity to drive thousands of PPC invalid clicks on a daily basis.
The secret sauce, IP address, also acts as a potential threat. Bot farms are detected by the device activity. When suspicious activity is detected, the IP address is the first thing that’s checked and that’s how bot farms are detected.
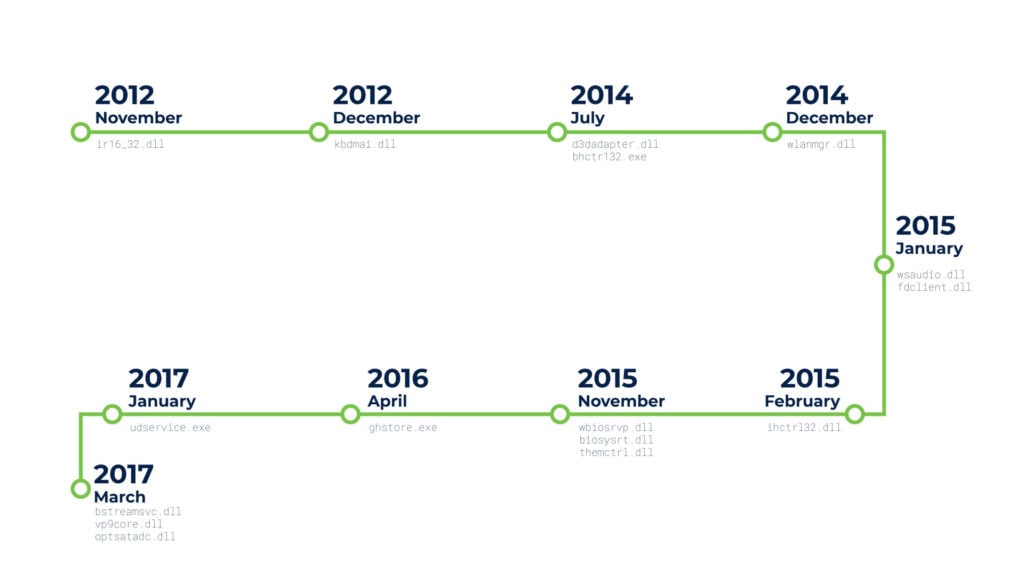
Historical Data on Click Bots and Bot Farms
The first click bot was identified in 2006. However, click fraud was used well before 2006. Historical data shows that click bots were identified as early as 2003 but due to lack of research, these weren’t identified and reported properly.
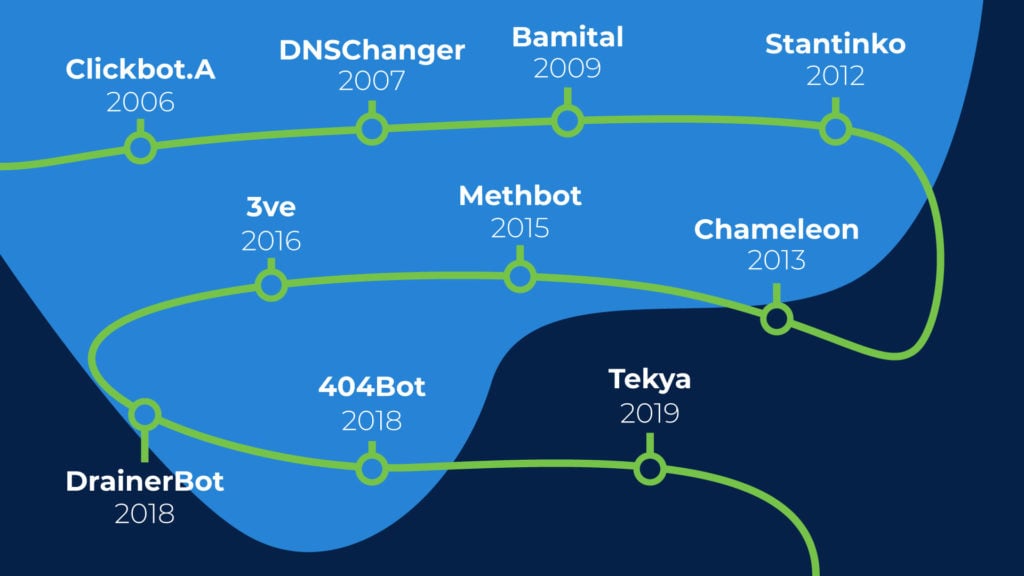
Here is the historical data of the well-known click bots and bot farms that are known and reported:
1. Clickbot.A
Google identified it in 2006. It used to target search ads and over 100K machines and devices were infected or linked to Clickbot.A and its botmaster. It was responsible for $50K+ ad fraud.
2. DNSChanger
A bot farm that was based on botnet and infected over 4 million computers was developed by Estonian hacker Vladimir Tsastin. DNSChanger ran for 4 years (2007-2011) and resulted in a loss of $14 million. It used to change the web address in the browser of the infected devices. Showing their own domains and ads to the users helped the hackers earn a commission from the ad networks.
3. Stantinko
Stantinko is a bot farm that’s quite versatile and has evolved over time. It was identified in 2012 and is still active today. It has infected more than 500K devices mostly in Russia. It originally started as malware in Chrome extensions where it used to perform ad injections. The software infected by the malware used to click ads that were mostly hidden, and the user never knew about the existence of the ads.
Stantinko is still active today and it has evolved a lot. It now has the potential to install additional malware and is now capable of accessing WordPress sites.
4. Bamital
It was a botnet that infected more than a million devices and was active between 2009 and 2013. Bamital was identified by Microsoft in 2013. It used to intercept search ads on Google, Bing, and Yahoo and redirected users on its own malware embedded websites.
It is estimated that it cost over $1 million per year to advertisers and the same amount was earned by the developers.
5. Chameleon
Chameleon was the very first botnet that targeted display ads. It was identified in 2013 and estimated to earn $6 million per month for the developers. It infected 120K devices and 202 websites. It used to perform ad clicks on the selected 202 websites.
6. Methbot
Methbot was one of the biggest bot farms ever detected. It remained active from 2015 to 2017 but it used to cost more than $3 million per day consistently to the advertisers. Methbot was powered by highly sophisticated infrastructure including 1900 dedicated servers, data centers, and more than 800K IP addresses. It used to create fake websites and webpages that looked real. Users watched ads on the fake websites and the bot farm owner used to earn money from the publishers.
7. 3ve

Also known as Eve was developed by the same Russian and Kazakh team that developed Methbot. 3ve is one of the most sophisticated bot farms ever developed and is still active today. It has control over 1 million IP addresses and more than 700K devices are infected at any given time. It works like Methbot by showing video ads to users on fake websites that look real in most cases.
However, 3ve has evolved and adapted over time. It uses existing malware and clicks bots and it copies human behaviour making it hard to detect.
It is still active and alive today and has resulted in click fraud of over $29 million.
8. DrainerBot
DrainerBot was identified in 2018 and it infected well over 10 million Android devices. It was distributed via several Android apps. The DrainerBot used to deliver invisible video ads to the device making millions for its developer. The video ads were never shown to the device user. The worst part: It consumed mobile data (up to 10GB/month) for video ad impressions and clicks.
The good news is that it has been identified and all the apps were removed by Google from its Store by 2019.
9. 404Bot
It is a bot farm that targets ads.txt and generates fake browser and click data and steals millions from advertisers. 404Bot targets publishers having large ads.txt files and it is estimated it resulted in click fraud of $15 million by February 2020 since its detection in 2018.
It is a sophisticated bot farm just like 3ve. It relies heavily on domain spoofing and showing fake URLs to users with ads and earns commission. Unfortunately, it is still active today.
10. Tekya
It is a mobile malware click bot that works like DrainerBot. Tekya was first identified in 2019. It infected around 56 Android apps and has over a million downloads. It runs ads in the background without the user’s knowledge using mobile data. The infected apps were removed from the Play Store by 2020.
How to Stay Safe from PPC Click Fraud?
So what options do you have to save your PPC campaigns from bot farms and invalid clicks?
The simple solution is to use a highly sophisticated and powerful click fraud detection and prevention tool. The click fraud detection and prevention tool you use must have a systematic and transparent approach to detecting and filtering invalid clicks that are generated by bot farms and click bots.
In an event, if the click fraud protection tool blocks legitimate IP addresses, you’ll lose potential customers. And this is even worse than having invalid clicks.
ClickGUARD, for instance, links with your Google Ads account and monitors ad clicks. It filters clicks based on historical data, user behaviour, IP addresses, and strong algorithms. The best part: It is transparent and shares all the data. It shows you the exact IP addresses it has blocked or will block.
Getting invalid clicks on your ads is something normal these days. What steps you take to safeguard your campaigns is essential.
Remember, the hackers who run million-dollar bot farms earning millions on a daily basis know the ins and outs of programming and hacking. They’re very smart. You need to be smarter, and the fraud detection tool you use must be transparent and current.
Else, you’ll keep losing money without getting a hint of it – ever.